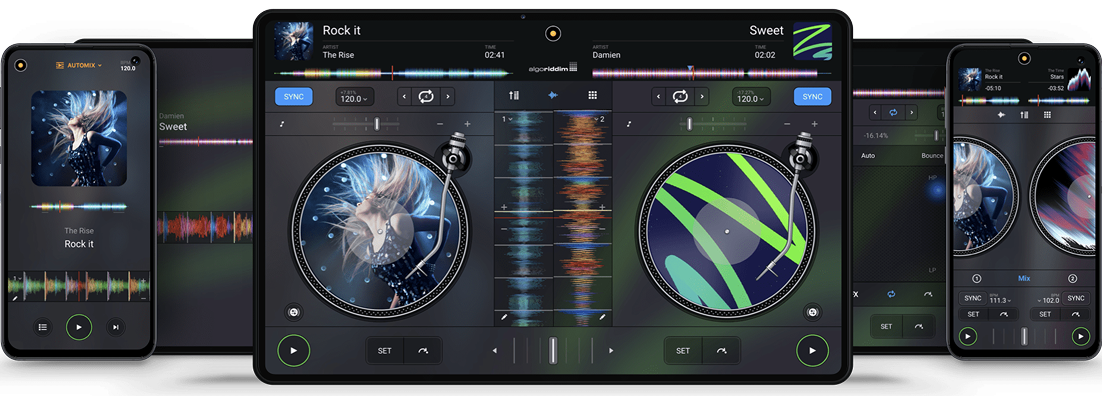
The #1 DJ app on Android
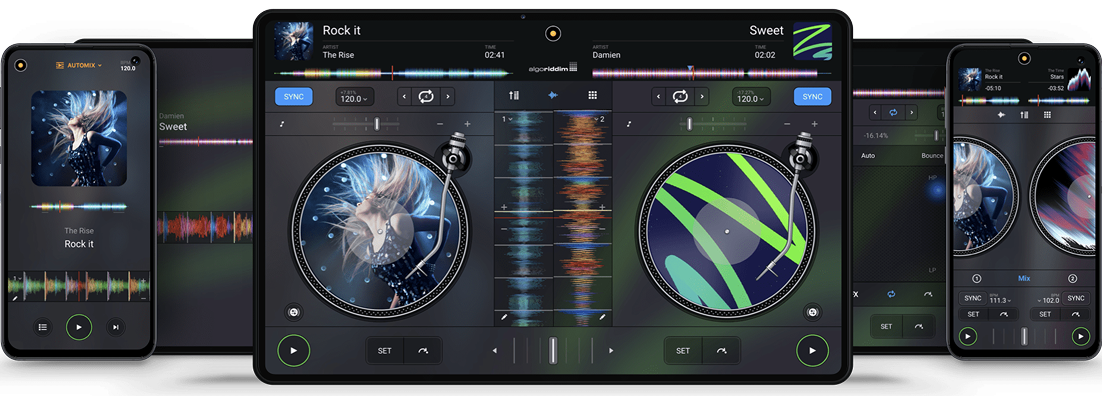
The #1 DJ app on Android
Requires Android 10 or newer • Release Notes
djay transforms your Android device into a full-featured DJ system. Seamlessly integrated with Spotify and Apple Music, djay gives you direct access to millions of songs. You can perform live, remix tracks, or enable Automix mode to let djay create a seamless mix for you automatically. Whether you are a professional DJ or a beginner who just loves to play with music, djay offers you the most intuitive yet powerful DJ experience on an Android device.
: The "c.io" in your query may refer to a specific domain or internal shorthand used by the attackers or security researchers to identify the target organization.
: If you know the company name associated with the "c.io" or Akira breach, searching for "[Company Name] Akira ransomware report" will likely lead you to the corresponding technical paper or news article.
: Akira is a well-known cybercriminal group that uses double extortion tactics, encrypting a victim's files and threatening to leak sensitive data on their Tor-hosted leak site if a ransom is not paid.
The filename typically refers to a collection of data logs associated with the Akira ransomware group , often appearing on data leak sites or cybersecurity forums where victim data is published.
Files found on leak sites or in zip archives from unknown sources may contain malware or personally identifiable information (PII) . It is highly recommended to only access these via a sandbox environment if you are a security researcher. Q2 2025 Ransomware Trends Analysis: Boom and Bust - Rapid7
In this context, the "paper" you are looking for likely refers to a , threat intelligence report , or incident analysis that documents the breach or explains the contents of those specific logs. Potential Context of the File
: Major security firms like Check Point or Rapid7 frequently publish detailed "papers" on ransomware strains and their specific leaks.

Lean back and listen to an automatic DJ mix with stunning transitions. Automix AI intelligently identifies rhythmic patterns including the best intro and outro sections of songs to keep the music flowing.
: The "c.io" in your query may refer to a specific domain or internal shorthand used by the attackers or security researchers to identify the target organization.
: If you know the company name associated with the "c.io" or Akira breach, searching for "[Company Name] Akira ransomware report" will likely lead you to the corresponding technical paper or news article. 835 logs (c.io AKIRA).zip
: Akira is a well-known cybercriminal group that uses double extortion tactics, encrypting a victim's files and threatening to leak sensitive data on their Tor-hosted leak site if a ransom is not paid. : The "c
The filename typically refers to a collection of data logs associated with the Akira ransomware group , often appearing on data leak sites or cybersecurity forums where victim data is published. The filename typically refers to a collection of
Files found on leak sites or in zip archives from unknown sources may contain malware or personally identifiable information (PII) . It is highly recommended to only access these via a sandbox environment if you are a security researcher. Q2 2025 Ransomware Trends Analysis: Boom and Bust - Rapid7
In this context, the "paper" you are looking for likely refers to a , threat intelligence report , or incident analysis that documents the breach or explains the contents of those specific logs. Potential Context of the File
: Major security firms like Check Point or Rapid7 frequently publish detailed "papers" on ransomware strains and their specific leaks.
Sign up for our newsletter
I would like to read about the latest and greatest on the djay product line by Algoriddim. If I should change my mind, I can unsubscribe at any time. Further information can be found in the privacy policy.