: GootLoader often creates a scheduled task or a registry key in HKCU\Software\ to maintain access after a reboot. Recommended Actions
: The user extracts the .7z file and double-clicks the .js file, believing it is a document.
: Perform a deep scan using an EDR (Endpoint Detection and Response) tool to identify registry-based persistence.
: Connections to compromised WordPress sites used as C2 infrastructure.
: Downloader / Initial Access Vector (GootLoader). Execution Chain
: Once executed via wscript.exe , the script reaches out to a Command and Control (C2) server to download the next stage, which often includes Cobalt Strike or fileless malware that resides in the registry. Technical Indicators Parent Process : explorer.exe or 7zFM.exe (extraction). Active Process : wscript.exe (executing the script).
: The JavaScript uses heavy obfuscation (junk code, reversed strings, and large arrays) to bypass signature-based antivirus detection.
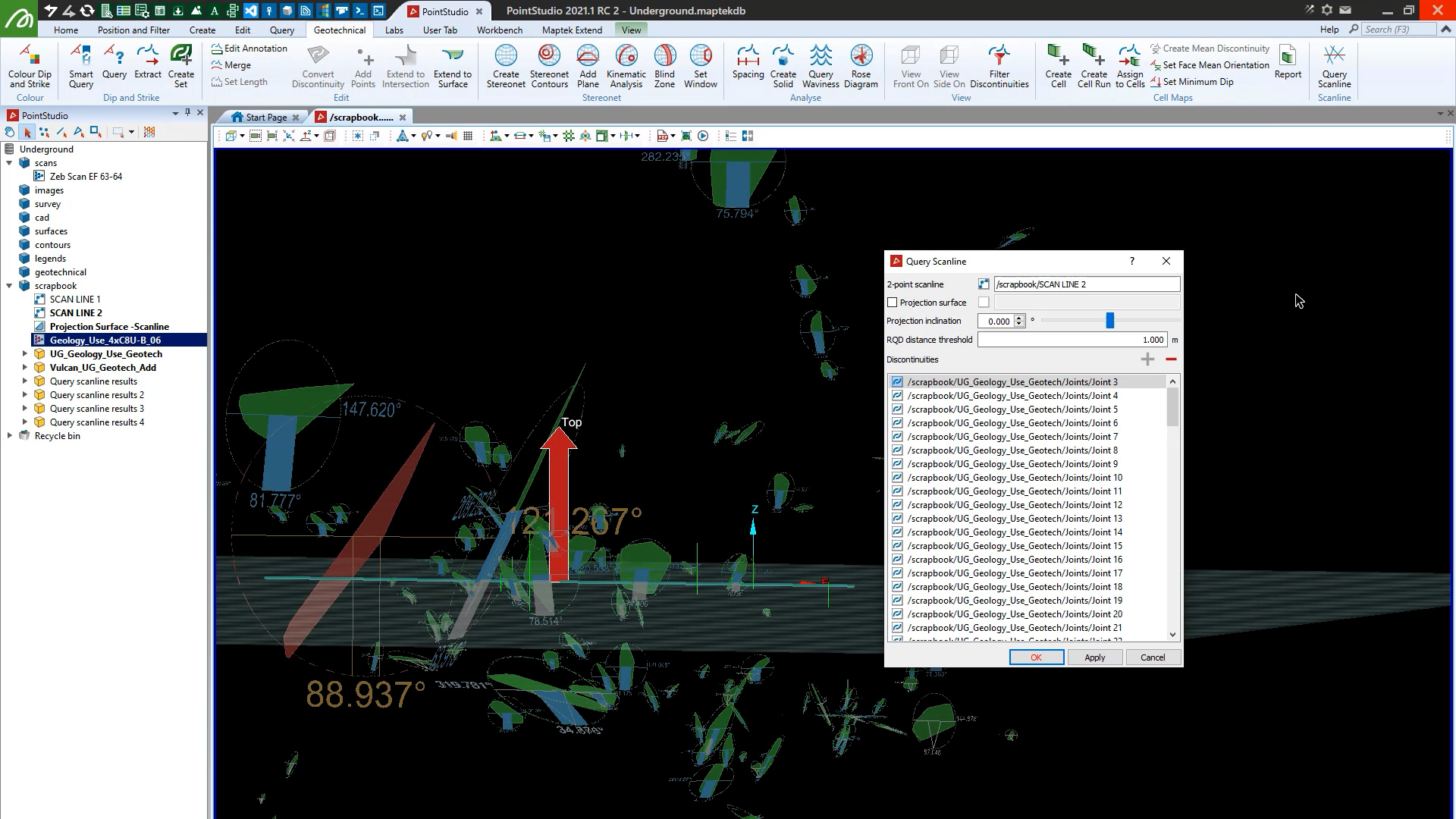
PointStudio 2021.1 features enhanced Inter-Ramp Compliance, performance and stability, supports Maptek R3 mkII laser scanners and enables unwrapping and colouring lines by grade and RQD calculation on scanlines.
: GootLoader often creates a scheduled task or a registry key in HKCU\Software\ to maintain access after a reboot. Recommended Actions
: The user extracts the .7z file and double-clicks the .js file, believing it is a document.
: Perform a deep scan using an EDR (Endpoint Detection and Response) tool to identify registry-based persistence.
: Connections to compromised WordPress sites used as C2 infrastructure.
: Downloader / Initial Access Vector (GootLoader). Execution Chain
: Once executed via wscript.exe , the script reaches out to a Command and Control (C2) server to download the next stage, which often includes Cobalt Strike or fileless malware that resides in the registry. Technical Indicators Parent Process : explorer.exe or 7zFM.exe (extraction). Active Process : wscript.exe (executing the script).
: The JavaScript uses heavy obfuscation (junk code, reversed strings, and large arrays) to bypass signature-based antivirus detection.
We use cookies to enhance your browsing experience and analyse our traffic. By clicking "Accept all", you consent to our use of cookies. You can customise your cookie preferences by clicking 'Customise Preferences'.
We use cookies to enhance your browsing experience and analyse our traffic.
Our website may store cookies on your computer in order to improve and customise your future visits to the website. By using cookies, we can track information about your usage of the site and improve your experience with anonymous and aggregated user data.
Review our Privacy PolicyEssential for the website's functionality, without which the site cannot operate smoothly. 02279.7z
Remember user preferences and choices to provide a more personalized experience. : GootLoader often creates a scheduled task or
Collect data on how users interact with the website, helping to improve user experience. : Connections to compromised WordPress sites used as
Used to deliver targeted advertisements to users based on their browsing behavior and preferences.